Contracts don’t just spell out the rights and obligations between the contracting parties, they’re also a gold mine of data—a lot of which are governed by privacy laws. How your organization and the third parties you partner with handle customer data is critical and can expose you to liabilities.
In this article, we’ll look at how contract lifecycle management (CLM) software can help you ensure your organization’s contract management practices comply with existing privacy regulations and also help you comply with any regulations that might surface in the future.
Key changes introduced by major privacy laws
General Data Protection Regulations (GDPR)
The GDPR governs how businesses will handle the personal data of European Union’s citizens or residents — whether these businesses are based in the EU or not. The GDPR created a buzz on arrival and is touted as the toughest privacy and security law in the world.
Under the GDPR, businesses must get consent for the use of the personal data of customers. Using the data is restricted to the specified purposes. The data the business collects must be only what the business needs.
GDPR requires that organizations incorporate “appropriate technical and organizational measures” in their processes and not as an afterthought. Organizations must also provide evidence of compliance by keeping records of their data processing, which they must provide on-demand by the regulatory authority.
The GDPR also requires organizations to notify the regulatory body of any data breach within 72 hours after they realize it. Where the breach exposes individuals to high risk, those individuals must also be informed.
California Consumer Privacy Act (CCPA)
The CCPA was enacted in January 2020, and it is the first law in the United States to set privacy regulations for businesses.
The CCPA protects every natural person who is resident in California. Under the CCPA, individuals have the right to know what personal information a business has on them and how that information is used. The law also gives individuals the right to opt out of the sale of their data and demand a copy if they want.
Unlike the GDPR, the CCPA applies to every organization that:
- Has a gross revenue of $25 million or more.
- Collects personal information on more than 50,000 individuals or households.
- Makes up to half of its yearly revenue from selling personal data.
In November 2020, the California Privacy Rights Act (CPRA) amended the CCPA to restrict the organizations the privacy law governs to those that collect personal information on at least 100,000 individuals or households — and, of course, those that fall within the other two criteria.
The CPRA further empowers individual customers to restrict the commercial use of their data by companies to terms they explicitly consented to.
It’s important to note that under the CCPA, companies had a 30-day window to comply with the law when regulators warn them about a breach. The CPRA, however, removed this grace period. Companies will face penalties immediately without the opportunity to put their house in order.
Other privacy laws in the United States
Additional states in the U.S. have passed similar privacy laws. Nevada, for example, enacted its Senate Bill 220 Online Privacy Law, while Virginia lawmakers passed the Consumer Data Protection Act (CDPA). If your business is located in these states, you’ll need to ensure it’s in legal compliance with these laws.
By contrast, on the national level, there is no uniform privacy law like the EU’s GDPR, although there are some privacy rules.
The Health Insurance Portability and Accountability Act (HIPPA), for instance, contains regulations on who can have access to your health information — also known as the protected health information (PHI). Under HIPPA, the sale or use of PHI for marketing requires explicit consent.
There’s also the Children’s Online Privacy Protection Act (COPPA), which regulates how companies collect information from minors online.
Privacy law issues to look out for
Evidence of data practice
It’s not enough to comply with regulatory requirements, you need to be able to provide evidence of such compliance. According to data privacy expert Debbie Reynolds:
“Evidence of data practices is essential because regulators want information about how companies handle data and their processes and procedures. They also want proof of actual data practices. As a result of technology and the fact that data can be tracked and traced, businesses must go beyond just creating documentation.”
To legally comply with privacy laws, your organization must keep records of data processing activities. This will include:
- The data you are using
- Where it’s processed
- How it’s processed
- What the data is used for
Assessing third-party data risk
Privacy regulators want to know how your business uses the customer data it collects. This spans across several areas, from requiring that data be collected and used with the consent of the individual customer to explicitly stating the rights individuals have to opt out of their data being sold or used for commercial purposes.
There may be legitimate reasons why your business will need to share the customer data you’ve collected with third-party partners. You need to ensure that you obtained the consent you need to do so, and your customers are adequately protected from unauthorized use of their data by the third party.
How you handle legacy data
Legacy data is information you have about your customers that’s no longer as valuable as it used to be. This could be because the information’s no longer up to date, or it’s stored in obsolete systems or formats.
Privacy regulations require that you collect data for a purpose and delete or return them to the owners once you’re done using them.
Data protection by design and default
Privacy regulations require that in everything you do in your organization, you must consider data protection “ by design and default.” Privacy compliance requires that you’ll:
- Collect only essential information
- Delete the data as soon as it has served its purpose
- Restrict access to the data and
- Secure data with the latest technology
How CLM software helps with privacy compliance in contract management
Implementing privacy compliance in your organization’s contract management practice can be an arduous task. A contract lifecycle management software like Ironclad will make it easier in the following ways.
Identify contracts at risk
As more states pass privacy laws, keeping up with legal compliance can be a hassle. With CLM, you can easily identify the contracts that the new laws apply to with ease. Then, you can take the necessary steps to bring them into compliance with the new laws.
Automatically create an addendum
After you have identified the contracts at risk, with CLM, you can quickly create an addendum by answering some questions. The AI-powered CLM will help you create the addendum you need and send them to the counterparty for their signature. Without a CLM, this process could take months.
Define who’ll have access to contract information
Privacy regulations place a strong emphasis on how you process data and who has access to them. Your contracts contain sensitive information—from employees’ personal information to clients’ data.
CLM will help you restrict who has access to information on your organization’s contracts based on roles, departments, and contract type. You can ensure that employees only have access to information that they need to do their jobs and nothing more.
For instance, your sales team has no business with HR contracts. With CLM, you can set up your process to be in privacy compliance.
Have visibility on your contracts process for easy reporting
We said earlier that it’s not enough to simply comply with privacy regulations — that you must also show proof of actual compliance. Regulatory authorities can come calling any day, and you need to be ready for them. CLM keeps track of all your contracts management processes so you can provide evidence of the compliance measures you’ve put in place.
Security features a CLM should have
Privacy regulations require that your organization use the latest technology to secure your data. Look out for the following contract management security features before you chose a CLM:
- Cloud-based deployment. You need cloud-hosted CLM software that allows you to change your contract management security policies swiftly.
- Security certification. Security certification deals with how organizations handle sensitive and confidential information. Only use CLM platforms with at least SOC 1 and SOC 2 certifications.
- Penetration and vulnerability testing. You can’t be too careful with security measures. Periodic tests will reveal security weaknesses that can be exploited. Choose a CLM vendor that runs penetration and vulnerability testing at least once a year.
- Encryption. With encryption, you can prevent unauthorized users from having access to your contract data. You need a CLM that encrypts all data in transit (using TLS 1.2 or higher) and at rest (through AES-256).
- User permission. Use a CLM platform that allows you to set access to contracts based on job roles, departments, and the type of contract.
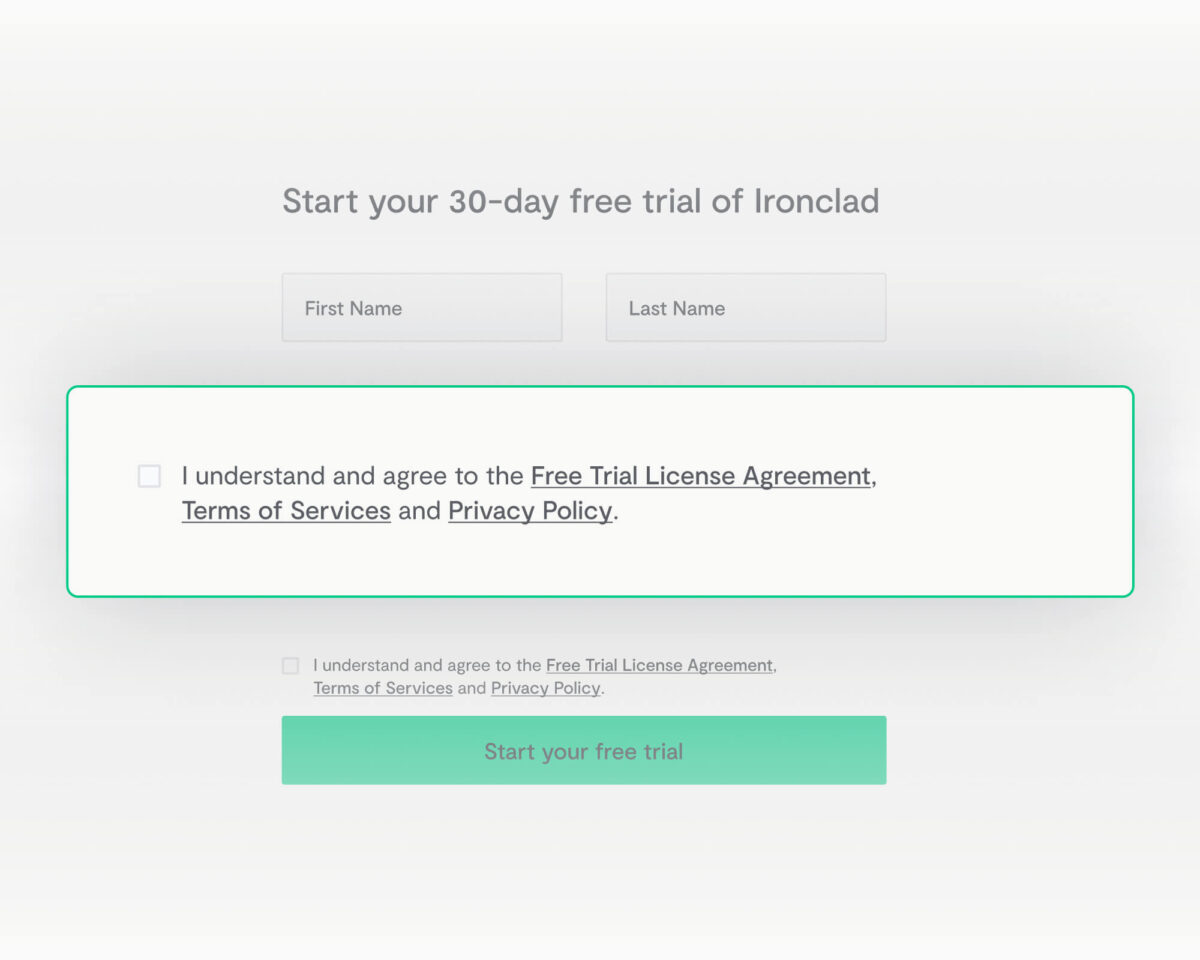
Ironclad’s CLM makes privacy compliance a breeze
Data privacy regulations are here to stay. They’ll only become stricter as privacy concerns continue to rise. With a lot of privacy regulations to keep up with, you need contract lifecycle management software that’ll help you to bring your contract processes in compliance swiftly, especially if your organization handles high-volume contracts. You cannot afford to take privacy compliance lightly.
Ironclad’s CLM has all the security features you need to bring your contracts process and how you manage your contracts data in privacy compliance.
Companies that take data security seriously use ironclad’s CLM. Discover how Ironclad ensures enterprise-level compliance for all their contracts with a free demo.
Ironclad is not a law firm, and this post does not constitute or contain legal advice. To evaluate the accuracy, sufficiency, or reliability of the ideas and guidance reflected here, or the applicability of these materials to your business, you should consult with a licensed attorney. Use of and access to any of the resources contained within Ironclad’s site do not create an attorney-client relationship between the user and Ironclad.
- Key changes introduced by major privacy laws
- Privacy law issues to look out for
- How CLM software helps with privacy compliance in contract management
- Security features a CLM should have
- Ironclad’s CLM makes privacy compliance a breeze
Want more content like this? Sign up for our monthly newsletter.